In a drive to add more things to home assistant, I found the unRAID API. This container provides unRAID server information to home assistant via MQTT. I figured this could be interesting to add to my stack, and potentially pretty useful in the long run, so I decided to get it going.
Continue reading “unRAID API and Home Assistant”Wood Working on the Gweike Cloud
Wood cutting and engraving is great on the Gweike cloud. As one expects from a CO2 laser, its much faster than the ortur I was using before and I had to play quite a bit to find some good settings for the new laser to optimize the performance.
Continue reading “Wood Working on the Gweike Cloud”Getting Started on the Gweike Cloud Pro
After having used a diode laser for a while, it had proven itself as a useful tool for my workshop. So what’s the next step to go from there, obviously a CO2 laser with more power and speed than the diode laser. I wanted a desktop model in the 50w+ range and found it in the Gweike cloud pro laser cutter. It has a similar feature set to other desktop models and supports LightBurn and local control (a major boon over the likes of GlowForge and despite the “cloud” part of the Gweike Cloud name).
Continue reading “Getting Started on the Gweike Cloud Pro”Building a Word Clock
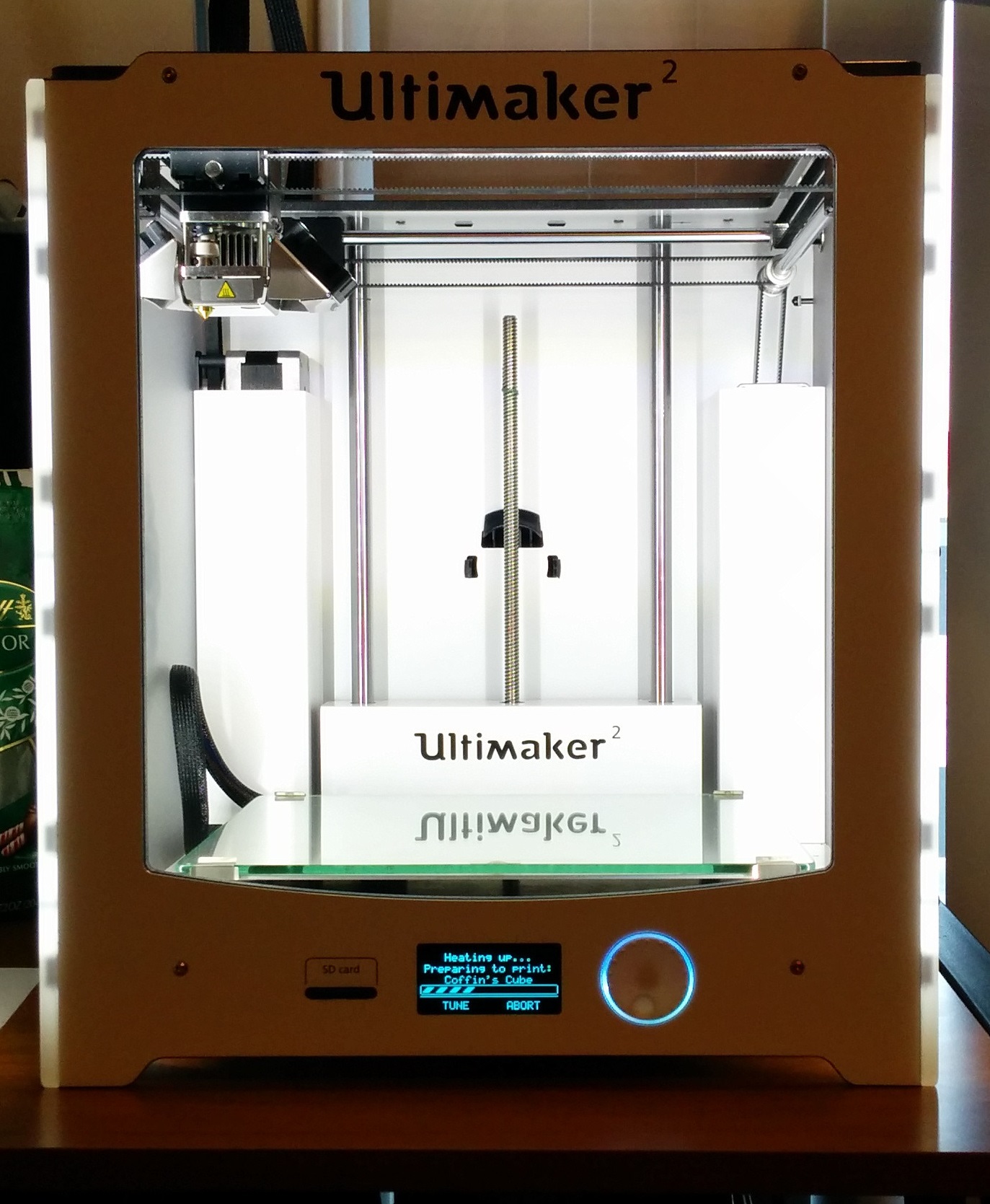
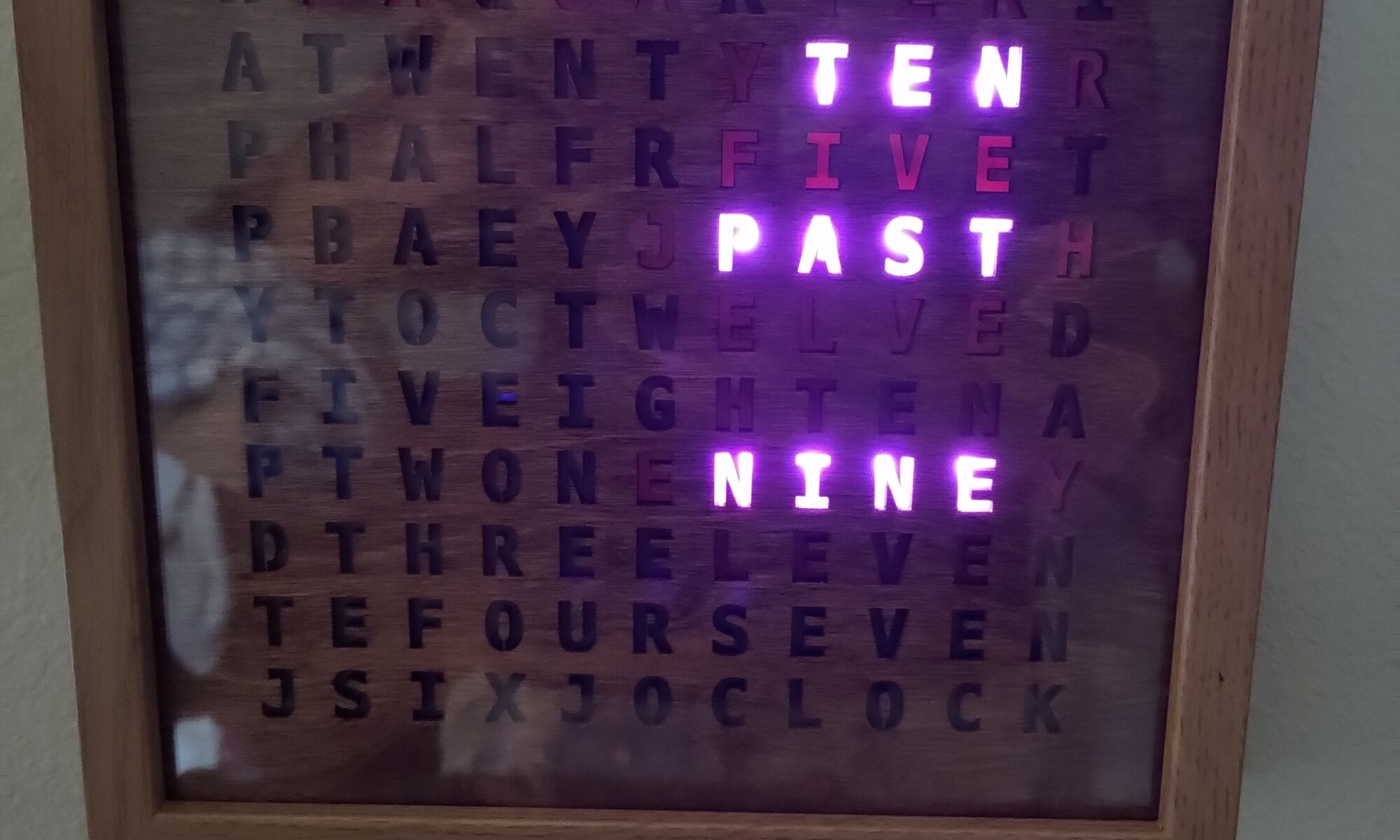
Way back around 2013, something started getting popular on Instructables, word clocks. They gave the time as a sentence instead of a usual number like most common clocks. I thought these were cool and wanted to build one, I even picked up parts, but never got around to building it.
Continue reading “Building a Word Clock”Using ntfy.sh from Home Assistant
While surfing Reddit one day I ran across a post about Unified Push and setting up ones own self hosted push notification system. A push notification system that can be self hosted and isn’t owned by any of the big tech companies, which I’m all for. So I decided to test it out by setting up home assistant notifications through it. While here I won’t be installing and setting up my own ntfy.sh server right now, I will probably be doing that part in the future.
Continue reading “Using ntfy.sh from Home Assistant”Getting SVG Data into CATIA
Another day, another type of data to import into CATIA. This time is the classic SVG format used by LightBurn and often edited with InkScape. This is pretty quick but I wanted a bunch of screenshots to make it easy to follow.
Continue reading “Getting SVG Data into CATIA”Network Layout
Here is a rough guide of how I have my network laid out. I haven’t really documented it before, so hopefully this covers the major points. I use a number of VLANS in my network to keep the IOT devices from being security threats, and prevent security devices from being able to access the internet (like security cameras).
I will write up a longer guide later on when I have some time, for now the short of it. The hardware is mostly Unifi gear with a Unifi controller running on my Proxmox host. This is the same host I run home assistant on (all virtual machines). The Unifi controller lets me configure my whole network in one pane of glass, its a bit of a pain at times, but for me the convenience has outweighed the higher price and limitations so far.
Continue reading “Network Layout”Fixing network problems in HASS
Recently I have been working on fixing the configuration issues in my home assistant installation. I run the supervised mode on an Ubuntu VM that I setup myself with some scripts (since it’s not supported by the official installer). Due to this, I encountered a problem with network manager in home assistant that caused home assistant to lose Internet access (so unable to download updates) even though the VM has no problems accessing the Internet as a whole.
Continue reading “Fixing network problems in HASS”Night Security Lights
I wanted to setup some smart lights to turn on and off at various times when I’m away so that it looks like people are still around in the house. These are going to be going between a few rooms to look more legitimate for anyone watching.
Continue reading “Night Security Lights”InkScape and LightBurn
Unable to Perform Path Operations
If you can’t do boolean operations in InkScape, you may have to un-group the paths. It can’t do path operations on groups, and sometimes InkScape will put a single object into a group. You can combine paths and do boolean operations on them that way, but that is using the path combine tool, you just cannot use the grouping feature.
LightBurn Limitations
You can’t use object operations on it for LightBurn to understand it. No use of object clip or mask should be used when creating files for use in LightBurn. You can make use of path difference or intersection to make changes to similar effect when avoiding the object tools.