I installed some new z-wave light switches recently and when working on one of them, I encountered a very peculiar problem, the light would turn on for one second, then flash off and back on again, repeating this constantly. I was unsure what was going on since I thought I had wired the switch correctly.
The switch box had 3 wires, 2 going up and out one side, and a third going up and out the other. This was in a closet with 2 lights in it, so I figured the two were for the lights and the third was for the incoming power. I was quite wrong. The two were for the incoming power (incoming power and the rest of that breaker) and the third was for the two overhead lights.
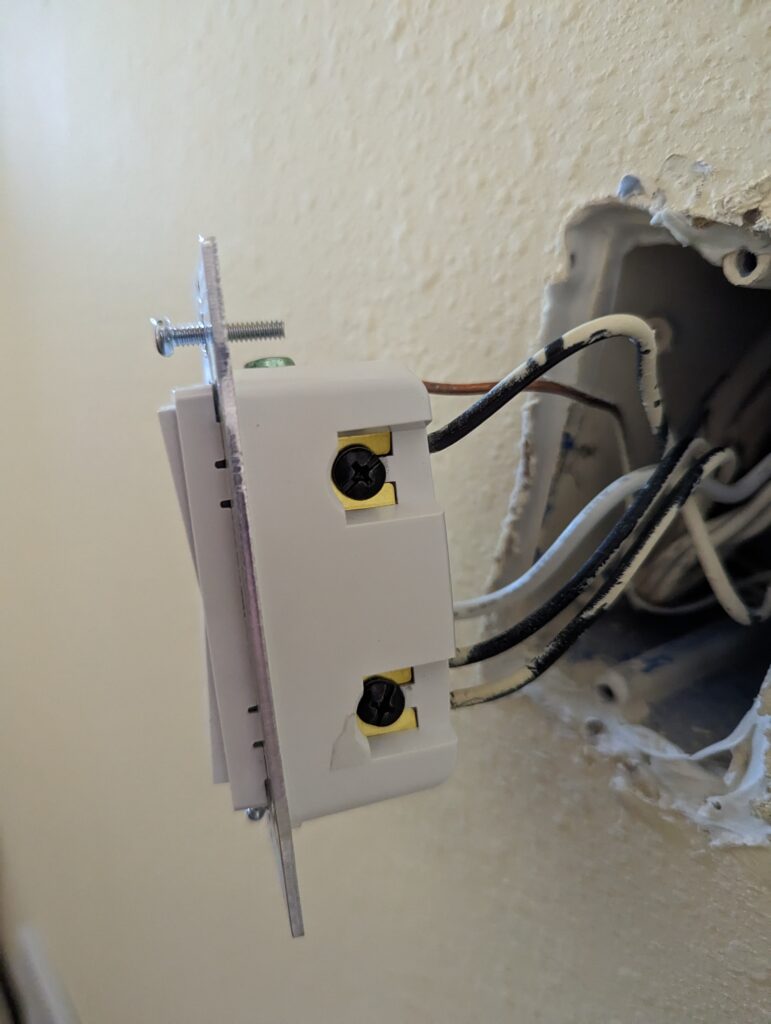
With it wired up correctly this time, the switch turned on and off correctly, no flashing on and off. I hadn’t seen a smart switch do this before, but now I know it was from receiving the line and the load.